What You See
A command center, not a confetti cannon of alerts.
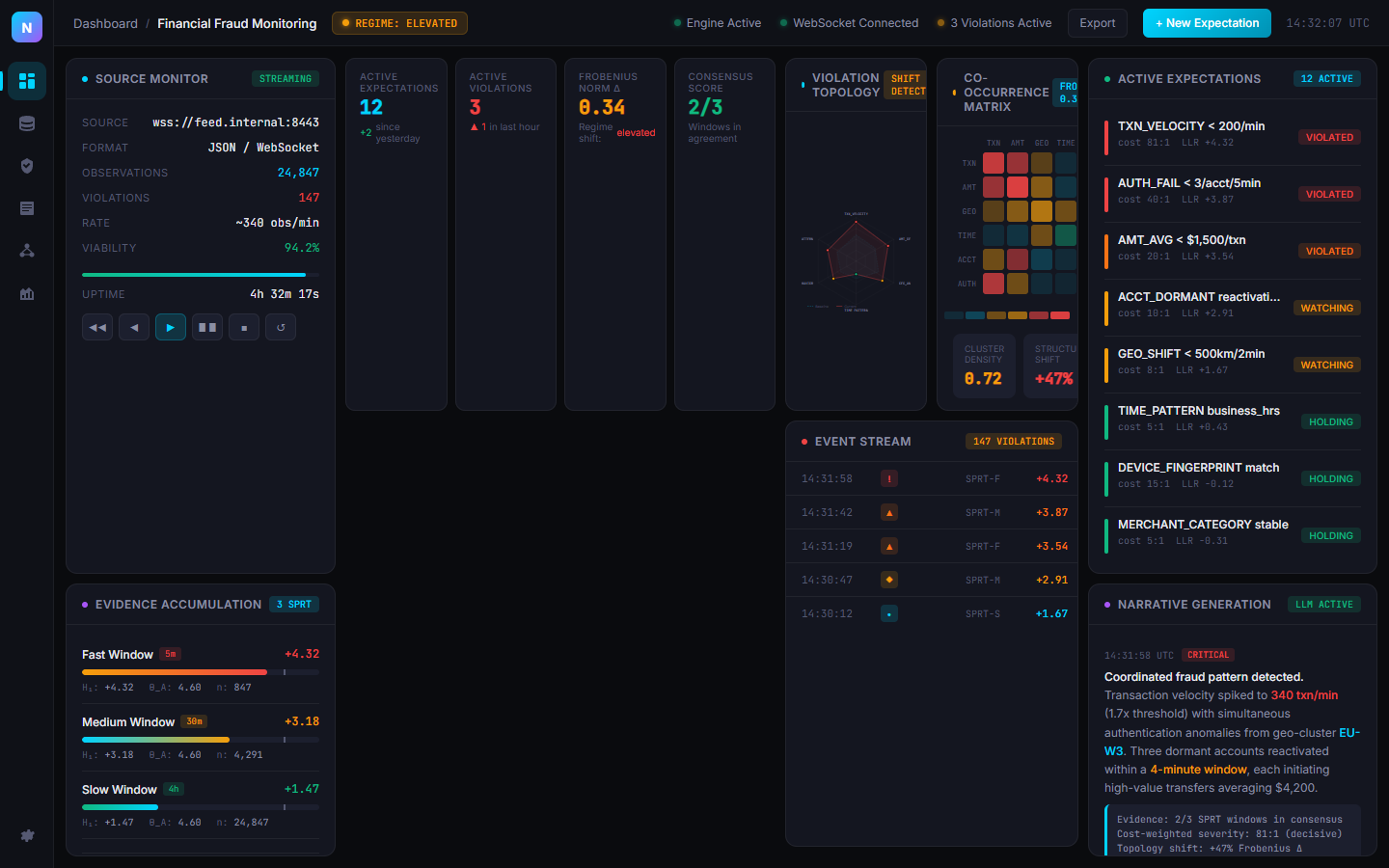
Source Monitor: Live WebSocket streaming status, observation counts, violation rates, viability scoring, and transport controls for streaming, stepping, or resetting your data feed.
Violation Topology: Radar chart showing violation magnitudes across all active expectations. Shape changes between baseline and current state reveal structural shifts before individual metrics do.
Co-occurrence Heatmap: Which expectations violate together. Structural tracking detects regime shifts in the violation graph structure — catching systemic patterns that per-variable monitors miss.
Narrative Generation: LLM-powered explanations of what changed, why it matters, and what to do next. Domain-gated security layer prevents prompt injection. Evidence-grounded, never hallucinated.
Every panel updates in real-time as data streams in. No refresh. No polling. No waiting.